Recently From the Blog
Blog Categories:
Improve Your Email Deliverability
We sent the following email to our Newsletter subscribers recently, but thought this information would be helpful as a blog post as well. On February 1, Yahoo and Gmail enhanced their requirements for mass email lists. Senders (especially those who email 5,000 users...
The Difference Between a Domain Name and a Website
In the digital age, where the internet plays a central role in our daily lives, it's essential to have a clear understanding of the fundamental components that make up the online world. Two of the most common terms you'll come across are "domain name" and "website",...
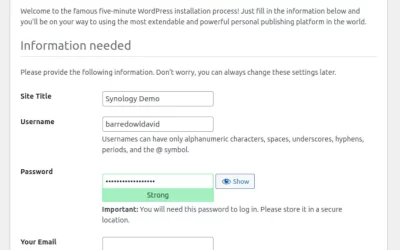
Launching a WordPress Website on Your Synology NAS
Synology Network Attached Storage (NAS) devices are extremely versatile. Not only do they support all of your typical network storage services such as SMB and NFS, but you can also install one or more packages to extend the functionality. These add-ons inclue DHCP,...
Five Free WordPress Plugins To Power Your Website
There are thousands of free WordPress plugins, so how do you choose which ones to use? Not every plugin is created equal. And like all software, they sometimes come with bugs - and even sometimes unintentionally introduce security vulnerabilities. Additionally, each...
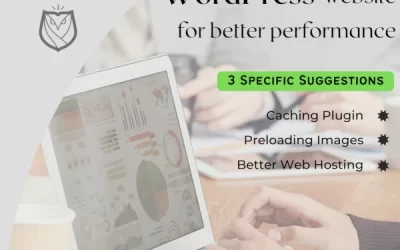
Tuning your WordPress website for better performance
According to Portent.com, websites should load in 4 seconds or less for optimal conversions. And according to Google, a website's bounce rate will increase over 30% if a pageload takes 3 seconds instead of 1 second. So for these reasons and more, it is imperative that...
5 Ways We Can Help Your Business
Maybe you’re a new business who needs help with your digital start-up, or maybe you just don’t have the time to keep your current website updated. Maybe you need a way for your employees to contact each other and clients without using their personal email address, or...
Why Does my Website Keep Crashing?
We've all been there. You are browsing a website, and maybe you are getting ready to purchase something, and suddenly that website stops working. This is always a frustrating experience. Or maybe this keeps happening to your own website, and your visitors are the ones...
WordFence Discloses Severe Vulnerabilities Affecting NinjaForms WordPress Plugin
On January 20, WordFence privately disclosed four serious security vulnerabilities to the developers of Ninja Forms, a popular WordPress plugin used by over 1 million websites. One of these vulnerabilities is rated a 9.9 on the Common Vulnerability Scoring System. A...
PCI Compliance: What, When Why and How?
Introduction Keeping your website secure is a crucial part of maintaining its overall health and reputation. Cybersecurity includes three things: Confidentiality, Integrity, and Availability. If your website cannot keep your visitors' data safe, it isn't secure...
Create Your New Website Using WordPress
A Content Management System (CMS) is software that makes it easy for website owners to update their websites. WordPress is one such CMS. And it powers over 30% of the websites on the internet today. In this blog post, I will introduce it, and will make some...
Security Changes Coming to a Website Near You
Websites, web servers, web browsers, and other software should be kept updated. Vendors such as Microsoft, Google, and Red Hat constantly release updates for their software. In this blog post, I’m going to discuss a few changes that might affect you. ADOBE FLASH END...
Fixing a Compromised WordPress Website
Like any content management system, WordPress is not immune to security vulnerabilities. The best way to recover from a WordPress compromise is to restore from a known good backup. You should always maintain proper backups (don't rely on a data sync, for example). But...